This blog post will take you through the steps of encoding a message using double transposition, just like British and American spies did in WWII. Should you feel like trying it out, it will be up to you to look up Morse code, secure a radio, and find someone to transmit it to.
Early in WWII, agents with SOE (a British wartime intelligence and sabotage agency) used what was called the poem code. Agents operating in northern Europe would pick a poem and memorize it. Agents operating in the Mediterranean area would often use novels, but the principle was the same. For this post, we’ll use Henry V’s St. Crispin’s Day speech, because I like it. In fact, I like it so much that my Shakespeare-quoting Englishman in Sworn Enemy and Deadly Alliance uses the band of brothers quote in both books. As an added bonus, Shakespeare’s copyrights have run out, so I can quote it on my blog without permission.
So here’s our code:
From this day to the ending of the world
But we in it shall be remembered
We few, we happy few, we band of brothers
For he today that sheds his blood with me
Shall be my brother; be he ne’er so vile,
This day shall gentle his condition.
And gentlemen in England now abed
Shall think themselves accursed that they were not here,
And hold their manhoods cheap whiles any speaks
That fought with us upon Saint Crispin’s Day.
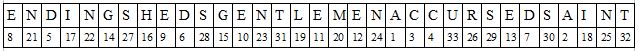
Now we need a message. For use with the poem code, a message needed to be at least 200 characters long. And it would be transmitted via Morse code, so no punctuation. Don’t read too much into this message—I’m just making stuff up. If you were really behind enemy lines, you’d be encouraged to mix up the language, but for this post, we’ll stick to English.
received latest drop need more detonators radio crystals and winter socks stop landing field compromised stop next moon period try field south of river stop agent taylor captured sent to fresnes stop malarkey cover blown request extraction at once stop plan to sabotage ball bearing factory in two weeks
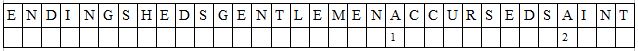
Next we need a key. For this part, we pick five words from our poem. Let’s choose these:
ending sheds gentlemen accursed saint
Next, we turn the five words into a numeric code. We assign a 1 to the first letter in the alphabet, then a 2 to the second, etc. If there are more than one of the same letter, give the letter farthest to the left the first number.
We’ll start with the A’s:
Then fill in the rest:
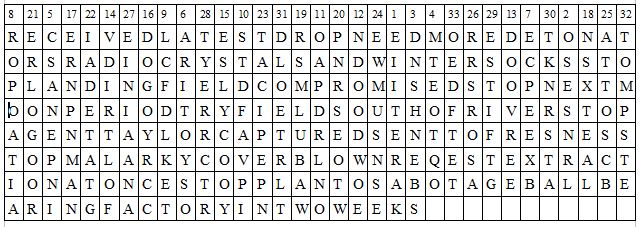
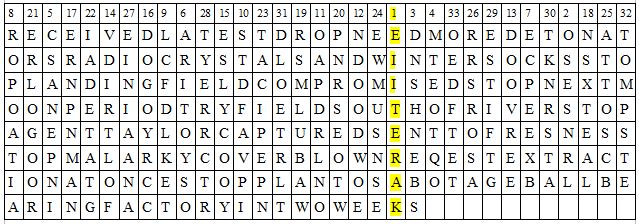
Our key has 33 letters in it, so next we draw a table with 33 columns in it. I’ll use the handy table generator in my word processing system, but if you’re in the field in the 1940s, you’ll probably have to draw your own squared paper. Then write your message inside, without any spaces between words.
Now comes the tricky part: transposing everything. First we’ll take our key and put it on top of our table.
Then we write out the new message, beginning with the first column and reading from top to bottom, then moving to the second column and so forth.
Here’s our new message:
EIITE RAKOS ESNRL DNSHN EBSMT EOTQO CSANE PNIAR ITOYS OECPE EXBRO POATI ALCFD LKETS TDFAV PIOAP DRLNO NDOOD WOEDO OVREE VDIRT LOFES LYCOO YDOGO YRCCE RNPNM ANNSX TEALR SMLUB AWPNR SEOTW ERLOG OORIA DETAT GTACI PEPNE WMUSN SEATT OSCBR RSROS AEINI AANAT YERRC TREST IFTGT KNRST ADLOE TRLTT OMPST EOEDF TET
I divided it into groups of five letters, because that was what they normally did. It made the message easier to manage during transmission. And it’s best to be on the air the shortest amount of time possible, because the Gestapo will be looking for you and your radio operator.
Now the message has been transposed once. But agents were using double transposition, so, you guessed it: time to repeat the process. Pick five different words from the poem and transpose the already transposed message again. (Savvy coders could probably take the letters from the first grid and place them directly into the second grid.) I’ll skip that step here. After the agent had the final transposition, they’d add an indicator so headquarters knew which words they’d used, hand it to the wireless operator, and hope the Gestapo didn’t catch them.
The poem code worked OK. But what if an agent was caught and tortured? The Gestapo could find out what their poem was and use it to help break past messages. Or what if German cryptographers cracked one message and figured out the words used as key? It wouldn’t be much of a stretch to figure out the poem from that, and then they could break all past and future messages.
Leo Marks, SOE’s head of codes, didn’t like the poem code. For one thing, it wasn’t as secure as he’d like it. For another, some of the agents in the field couldn’t spell very well, which fouled up their coding. He came up with what he called worked-out-keys, or WOKs. With WOKs, agents would have keys already made for them and printed on something easily hidden like a silk handkerchief. Each set of keys would be burned after use, so each message used a different key. Even the agents wouldn’t remember what their key had been, so the Gestapo couldn’t torture it out of them, thus making the messages more secure. WOKs also saved the agents the step of making their own keys, plus, it was considered secure with only 100 characters (down from 200), so the process was slightly less tedious. And no more misspellings (at least for the keys). The WOKs would look something like this:
18.9.11.4.20.10.21.22.3.6.13.1.17.23.14.7.19.8.12.15.5.16.2
in pairs, with an indicator group off to the side to tell headquarters which pair an agent was using.
So what brought this blog post up? Toward the end of last year I read Leo Mark’s memoir, Between Silk and Cyanide. It’s one of the best books I read in 2013 and I highly recommend it.
Then I re-read a WWII spy thriller that I’d read a few years before. The first time I read the novel, I thought it was pretty good. But the second time around, I noticed that the heroine was doing double transposition in her head. Yes, that entire process we’ve done above, plus the second transposition, without any scratch paper. She somehow figured out what she wanted to say, didn’t write it down, and magically transmitted it via Morse code, using both the poem code and her WOKs. No, this wasn’t a paranormal book, so the heroine wasn’t supposed to have superpowers.
The novel will remain unnamed in this post, but since reading it I’ve felt the need to explain how double transposition works. Have you ever wanted to set the record straight after reading a book that got it wrong? If you were transported back in time to WWII and became an agent in occupied Europe, do you think you’d have a handle on double transposition?
Very informative. Thanks for sharing it. 🙂
LikeLike
Thanks, Belsbror!
LikeLike
Wow. That is crazy complicated. I’m impressed. I’ll have to show this to my son who is a WWII nut. He’d totally get into this.
LikeLike
Let me know if your son likes it! If he’s a reader, he might enjoy “Between Silk and Cyanide.” It’s long, but well-written, informative, and sometimes funny. A little swearing, but it also includes some uplifting threads of courage and sacrifice.
LikeLike
He’s only 12, and he prefers non-fiction to fiction, but he’s read a ton of WWII books. Is that one fiction? I haven’t shown him your post yet, but I will. Crazy night. 🙂
LikeLike
It is nonfiction, but it might be a little old for a 12 year old. And it’s 600 pages. Here’s my goodreads review of the book: http://www.goodreads.com/review/show/477761578
LikeLike
Wow. It sounds amazing. I’ll have to keep it in mind for the future, when he’s up for 600 pages. Thanks for the tip, and good luck with that other world war. 🙂
LikeLike
Thanks, Rebecca!
(And about “Between Silk and Cyanide”. . . it was amazing, but since we’re talking about a teenager reading it, I feel I should warn you that the author didn’t have LDS standards. It doesn’t get detailed, but it’s there. And in an effort to thwart German code-breakers before WOKs came out, Marks had some of the codebreakers make up poems for the agents to use, and I remember at least one poem that was very crude. Just FYI. It’s a PG-13 book.)
LikeLike
Thanks for the heads up!!!!!!
LikeLike
I have found a several books over the years that make me want to “set the record straight”. My poor roommates have gotten an earful when I’ve needed to “correct” an error in a book.
Typically it goes something like this:
Me: “I need to complain about something for a moment.”
Roommate(s): *sigh* “Okay.”
Me: Detailing what the book said and then explaining what it should have said and why.
Roommate(s): “Do you feel better now?”
Me: “Much!”
So my question to you A.L. – Do you feel better now?
Also, I agree that doing double transpostition in your head is really far fetched, even if it is “only” 300 characters & you have a photographic memory &/or are a genius.
LikeLike
Yes, yes, I do feel better now. The same novel also had an Obersturmfuhrer (roughly a 1st lieutenant) bossing around a Captain and a Major. And now that I’ve pointed that out, I feel even better.
Feel free to call me if your roommates aren’t willing to listen to your complaints! I’d love to hear them.
LikeLike
I definitely wouldn’t have been the codebreaker back then. It makes my head hurt just going through all your steps.
LikeLike
Complicated and tedious, yes! And then decrypting it–yikes! Especially if the agent who coded it misspelled a key word or hatted/misaligned their columns. SOE employed lots of code breakers, and one of the things they looked for were people who loved music and crossword puzzles. (I wouldn’t have been hired.)
LikeLike
Neither would I have been hired. I can’t do a crossword without the cheat sheet at the back.
LikeLike
LOL. We all have different talents, don’t we? I haven’t attempted a real crossword puzzle for years. Maybe I should try one again sometime.
LikeLike
This thread of conversation about crossword puzzles & codes instantly made me think of the panic in 1944 when the answers to the Daily Telegraph’s crossword puzzle were Utah, Omaha, Mulberry, Neptue & Overlord – all code names for the cross channel invasion of France.
http://www.historic-uk.com/HistoryUK/HistoryofBritain/Crossword-Panic-of-1944/
LikeLike
Nice link, MG. I remember reading about the panic (in The Longest Day), but the footnote adds some interesting things I hadn’t heard before.
LikeLike
Are you sure your example is correct? Check the wikipedia page. You don’t rearrange the columns, you write them out line by line, then insert the new sequence into the new box and do the same procedure one more time.
LikeLike
Thanks for your comment, Chris. It looks like I need to go back to coding school! I’ve updated the post. Thank you for politely giving me the opportunity to make my blog (and my books) better.
LikeLike
Thanks! This was really informative. I’m in the middle of ‘Between Silk and Cyanide’ and this really cleared up the process which the FANYs used to decode the agents messages.
LikeLike
I’m glad it helped! Are you enjoying the book so far?
LikeLike
This is really interesting! I was looking up poem coding because I have to do a project on Marks poem This Life I Have in English and this cleared up a lot of confusion I had about the coding! I doubt I would ever be able to be a coder, but I think I managed to properly code my own poem 🙂
LikeLike
I’m glad the post was helpful and that you were able to complete some successful coding. Good luck with your English project!
LikeLike
I just have to wonder, how does anyone know what words are used to make the alpha-numerical bit at the beginning? I’ve been poem-coding for about a year now (just for my own personal amusement really, but I first learned about it for a school project) and I generally use short poems and skip codes, if I can manage it.
LikeLike
http://chris-intel-corner.blogspot.gr/2013/10/soe-cryptosystems-german-view.html
LikeLiked by 1 person
The link posted by Chistos T ought to give you more information, Rae. I hope that answers your questions.
LikeLike
It was fun to read. Thank you.
LikeLiked by 1 person
What a neat post! Gosh that encryption process fascinates me. It’s also fascinating how responsible it was for a lot of things in WWII!
LikeLiked by 1 person
Thanks, M.B.!
LikeLiked by 1 person
Thanks for a great post, as an ex Regimental Signal Sargent in a British Armoured Unit various codes were my daily staple diet, your post showed what our predecessors had to go through to transmit and receive information.
LikeLiked by 1 person
Thank you for your comment, Mr. Wainwright. I appreciate someone of your expertise taking the time to read and post about this.
LikeLike
Please, it’s ‘Morse’ code, not “Morris” code.
Otherwise, thanks for a good read.
LikeLike
Thank you, Phillip. I’ve corrected the spelling. I hope you’ll forgive my earlier lapse!
LikeLike
Great post, also Reading Silk and Cyanide and your post explains the process very well.
LikeLiked by 1 person
Thanks, Martyn! That’s a good book! I’m glad my post was helpful.
LikeLike
One of the books I read as a child:

I also enjoy historical fiction; notably The Only Thing To Fear by David Poyer
LikeLike
Historical fiction is one of my favorite genres. Both those books look interesting!
LikeLiked by 1 person